Supabase Auth vs Authgear for Next.js: Which Should You Choose?
Supabase Auth and Authgear are both production-ready for Next.js App Router — but they take fundamentally different approaches to authentication. This guide gives you a fair, practical comparison with a feature table, setup code for both, and clear guidance on when to choose each.



































_%20A%20Developer%E2%80%99s%20Guide%402x.jpg)





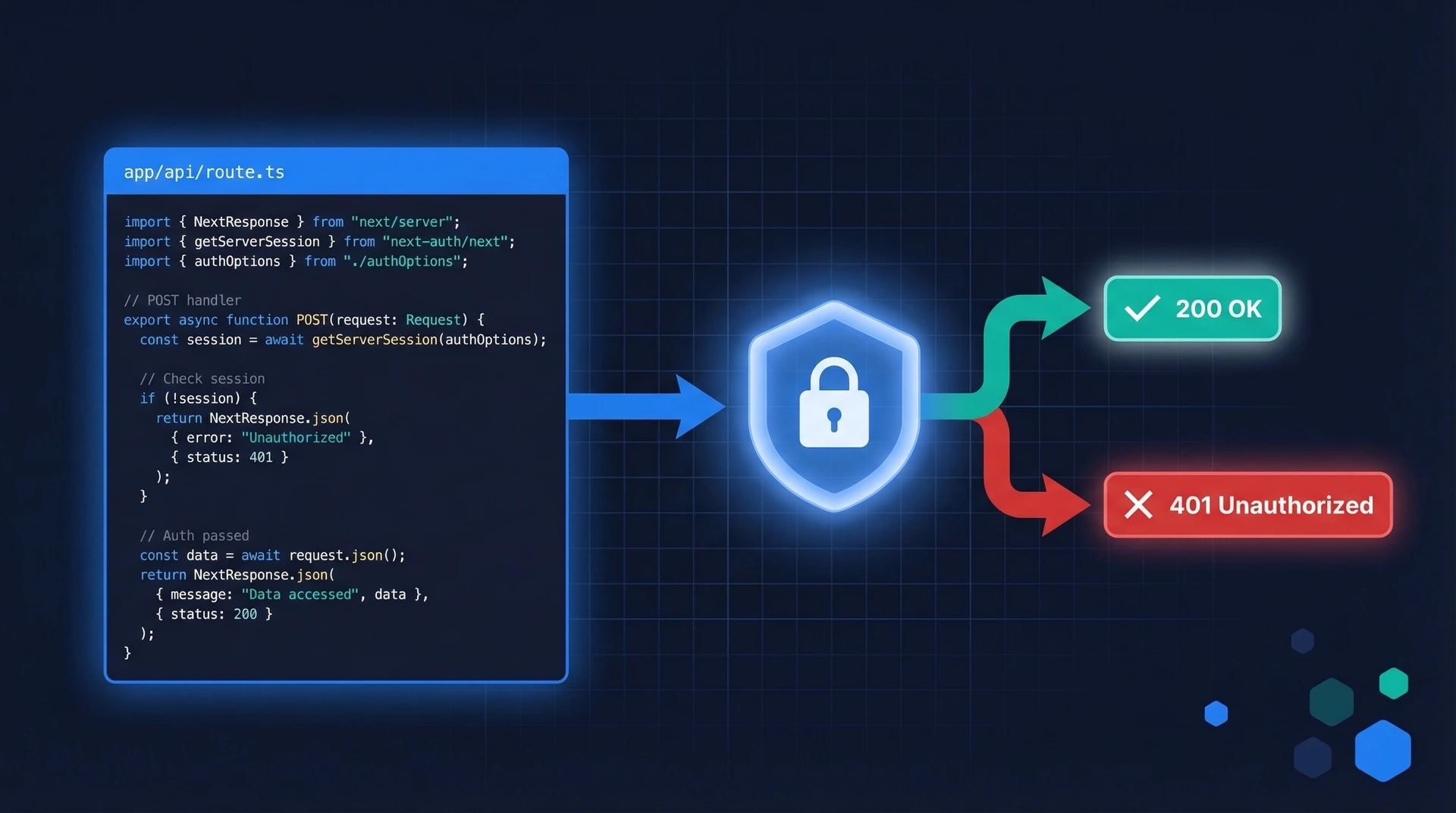
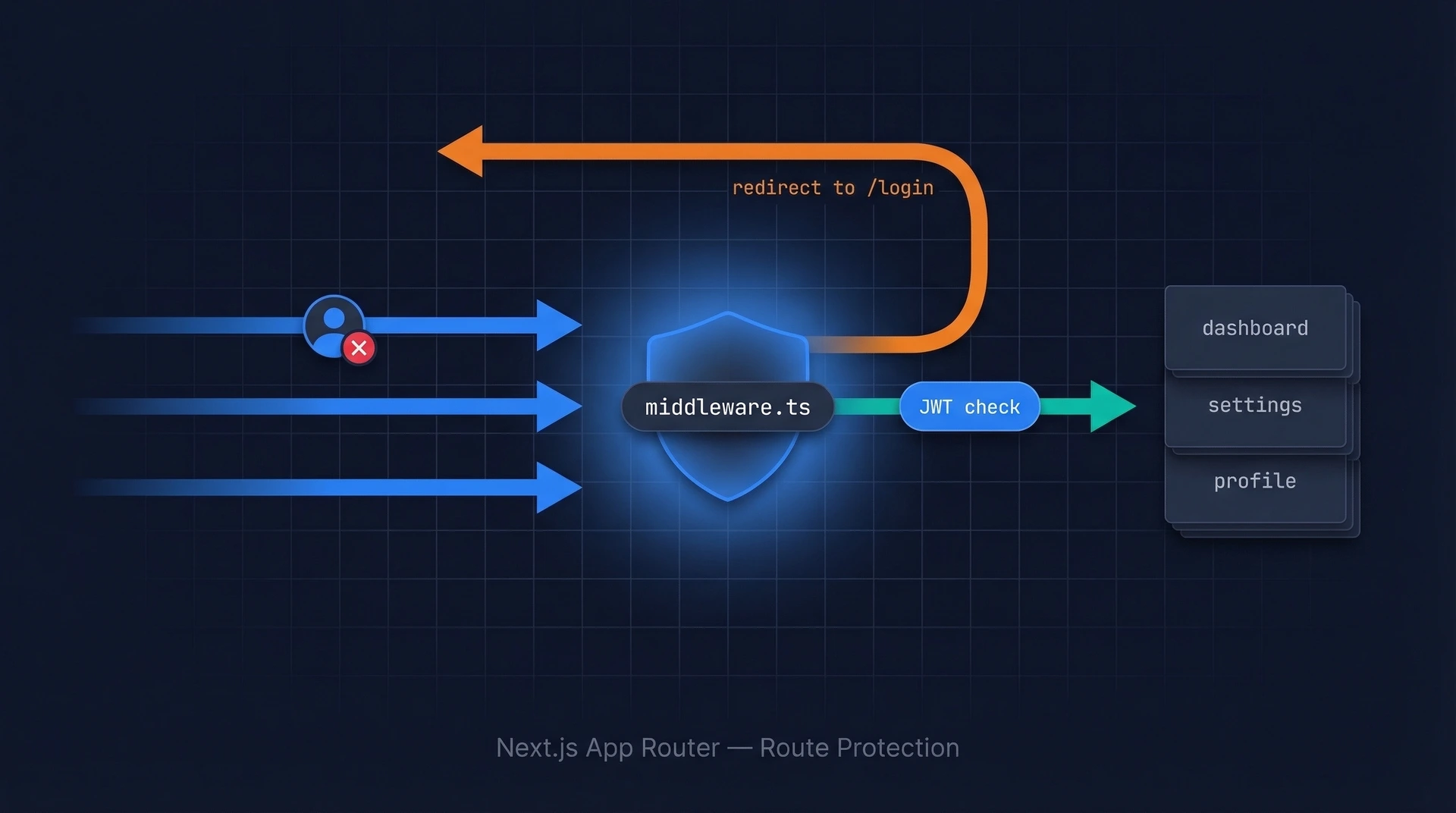
_%20Examples%20%26%20API%20Prevention%402x.jpg)
%402x.jpg)